The Vital Function of Information and Network Safety And Security in Shielding Your Details
In a period where information breaches and cyber risks are significantly common, the importance of durable data and network security can not be overstated. The application of efficient security procedures, such as security and gain access to controls, is crucial to preserving depend on and functional integrity.
Comprehending Information Security
In today's digital landscape, an overwhelming majority of organizations face the intricacies of data safety. This essential component of infotech involves securing delicate data from unauthorized accessibility, corruption, or theft throughout its lifecycle. Data safety encompasses numerous methods and technologies, including file encryption, accessibility controls, and data masking, all focused on securing info versus breaches and susceptabilities.
An essential aspect of data safety is the recognition and classification of information based on its level of sensitivity and significance. This category helps organizations prioritize their safety initiatives, assigning sources to shield one of the most crucial details effectively. Moreover, implementing robust plans and procedures is important to make certain that employees recognize their function in keeping information security.
Routine audits and assessments aid in recognizing potential weaknesses within an organization's information safety and security framework. In addition, staff member training is vital, as human error remains a significant consider data breaches. By cultivating a culture of safety awareness, organizations can reduce dangers related to expert hazards and oversight.
Significance of Network Safety And Security
Network protection stands as a cornerstone of a company's total cybersecurity method, with around 90% of organizations experiencing some type of cyber danger recently. The value of network safety and security depends on its capability to shield delicate details and keep the integrity of organization procedures. By safeguarding network facilities, organizations can avoid unapproved accessibility, data violations, and various other harmful activities that could endanger their properties and track record.
Executing durable network safety gauges not just assists in mitigating threats however likewise promotes trust among stakeholders and customers. When consumers are guaranteed that their financial and personal information is safe and secure, they are most likely to involve with the organization, leading to boosted client commitment and service development.
Furthermore, a well-structured network security framework helps with compliance with various regulative needs. Organizations needs to follow sector requirements and lawful mandates concerning data defense, and reliable network protection techniques can make certain conformity, consequently avoiding prospective charges.

Common Cyber Risks
Organizations have to remain vigilant against a range of cyber threats that can undermine their network safety initiatives. Amongst one of the most common hazards is malware, which incorporates infections, worms, and ransomware that can disrupt operations, steal data, or hold info captive. Phishing strikes, where destructive stars impersonate trusted entities to trick people right into disclosing sensitive info, continue to grow in sophistication, making customer education and learning crucial.
Another widespread danger is distributed denial-of-service (DDoS) attacks, which overload systems with official website traffic, making them inaccessible to reputable customers. Insider risks, whether deliberate or unintentional, position substantial risks as workers might unintentionally subject delicate information or intentionally manipulate their accessibility for harmful purposes.
Additionally, susceptabilities in software application and equipment can be exploited by cybercriminals, highlighting the importance of routine updates and spot management. Social design strategies additionally complicate the landscape, as enemies manipulate individuals into revealing confidential information with mental control.
As these risks advance, companies must preserve an aggressive strategy to recognize, minimize, and react successfully to the ever-changing cyber hazard landscape, safeguarding their useful information and preserving depend on with stakeholders. fft pipeline protection.
Ideal Practices for Protection
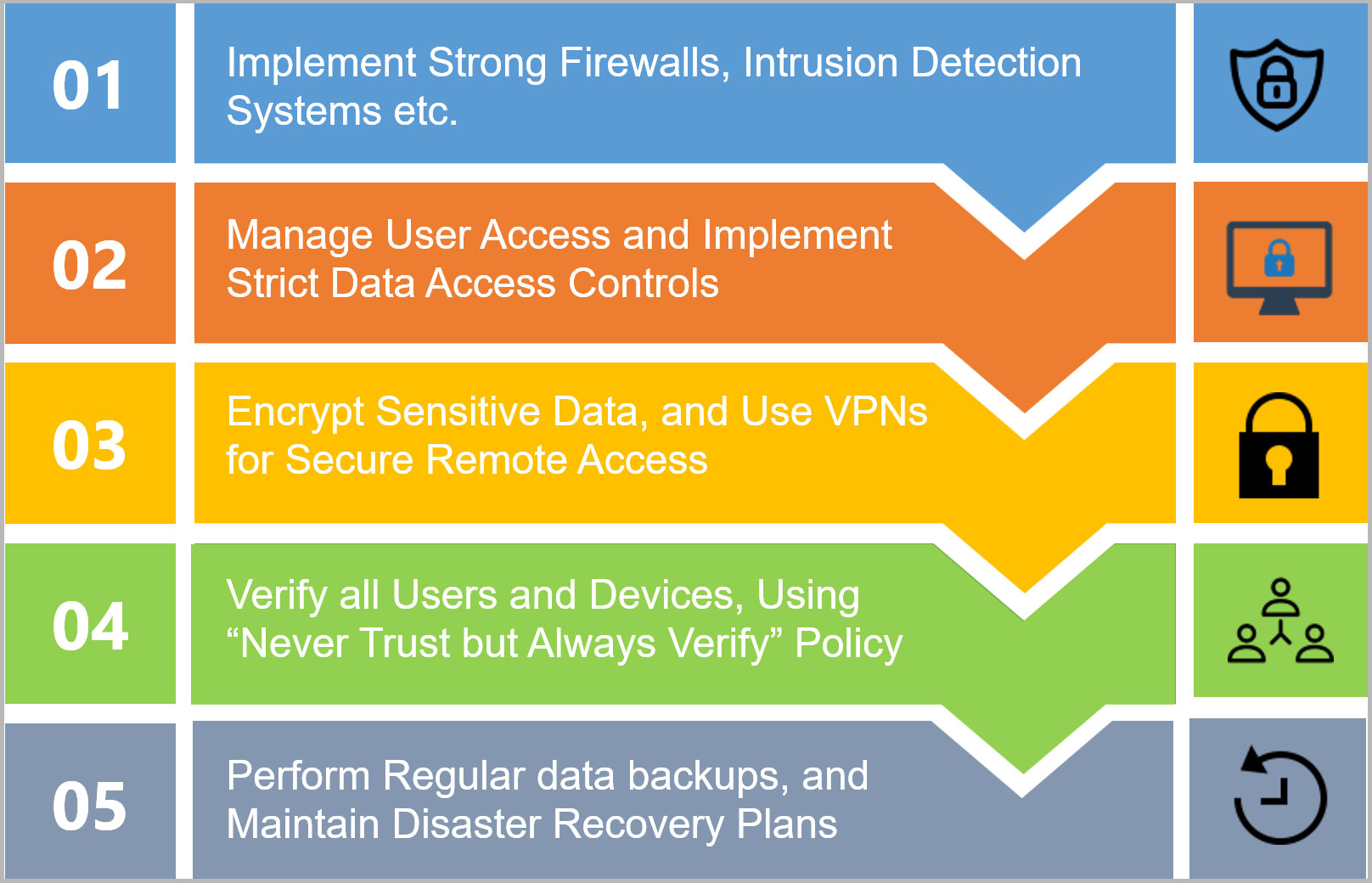
Carrying out durable safety and security steps is vital for guarding delicate info and keeping functional stability. Organizations must start by performing extensive risk assessments to recognize susceptabilities within their systems. This aggressive strategy allows the prioritization of security campaigns customized to the particular requirements of the organization.
Embracing strong password policies is important; passwords need to be intricate, routinely transformed, and took care of using pop over here protected password administration devices. Multi-factor verification (MFA) adds an extra layer of safety by requiring extra verification techniques, thus decreasing the risk of unapproved access.
Regular software application updates and spot management are critical to secure versus recognized vulnerabilities. Carrying out firewalls and breach detection systems can additionally secure networks from exterior dangers. Worker training is just as important; personnel needs to be educated on acknowledging phishing efforts and comprehending the significance of information safety procedures.
Information encryption should be utilized for sensitive info, both at rest and in transportation, to guarantee that also if data is obstructed, it stays unattainable (fft pipeline protection). Lastly, organizations must create and regularly examination event response intends to make sure speedy action in case of a security violation. By sticking to these best methods, organizations can enhance their safety and security posture and safeguard their essential information properties
Future Trends in Security
The landscape of information and network security is continually progressing, driven by improvements in innovation and the enhancing elegance of cyber hazards. As organizations progressively take on cloud computer and IoT gadgets, the standard of safety and security will change towards a zero-trust model. This technique highlights that no entity-- interior or exterior-- is naturally trusted, mandating confirmation at every access point.
Moreover, making use of fabricated intelligence and device discovering in protection protocols gets on the increase. These technologies enable predictive analytics, enabling organizations more info here to recognize susceptabilities and prospective risks before they can be made use of. Automation will likely play a pivotal duty in enhancing safety responses, lowering the time taken to mitigate violations.
Additionally, regulatory frameworks will remain to tighten up, necessitating a lot more rigorous conformity measures. Organizations has to stay abreast of advancing laws to ensure they satisfy safety and security requirements.
Verdict
To conclude, the significance of information and network protection can not be overstated in the contemporary digital landscape. With the frequency of cyber threats and the enhancing complexity of governing needs, companies have to embrace detailed security actions to protect delicate details. By remaining and implementing efficient techniques informed concerning arising trends, companies can enhance their strength versus potential strikes, guaranteeing information honesty and fostering depend on amongst stakeholders and clients. Focusing on safety remains vital for operational continuity and long-term success.
In an age where data violations and cyber risks are increasingly prevalent, the importance of robust information and network safety can not be overstated. Data protection includes different techniques and technologies, including file encryption, accessibility controls, and data masking, all aimed at guarding info versus violations and vulnerabilities.
An essential aspect of information protection is the recognition and classification of information based on its level of sensitivity and value.The landscape of data and network security is constantly advancing, driven by developments in innovation and the boosting class of cyber hazards.In final thought, the value of information and network safety and security can not be overemphasized in the modern digital landscape.